In the modern world of electronics, the term Digital is generally associated with a computer because the term Digital is derived from the way computers perform operation, by counting digits. For many years, the application of digital electronics was only in the computer system. But now-a-days, digital electronics is used in many other applications. Following are some of the examples in which Digital electronics is heavily used.
- Industrial process control
- Military system
- Television
- Communication system
- Medical equipment
- Radar
- Navigation
Signal
Signal can be defined as a physical quantity, which contains some information. It is a function of one or more than one independent variables. Signals are of two types.
- Analog Signal
- Digital Signal
Analog Signal
An analog signal is defined as the signal having continuous values. Analog signal can have infinite number of different values. In real world scenario, most of the things observed in nature are analog. Examples of the analog signals are following.
- Temperature
- Pressure
- Distance
- Sound
- Voltage
- Current
- Power
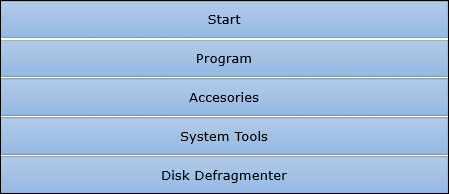
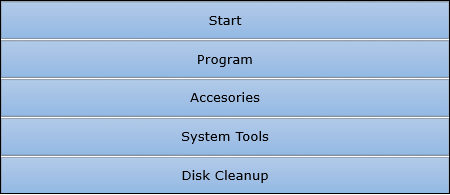
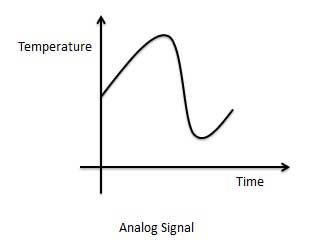
Graphical representation of Analog Signal (Temperature)
The circuits that process the analog signals are called as analog circuits or system. Examples of the analog system are following.
- Filter
- Amplifiers
- Television receiver
- Motor speed controller
Disadvantage of Analog Systems
- Less accuracy
- Less versatility
- More noise effect
- More distortion
- More effect of weather
Digital Signal
A digital signal is defined as the signal which has only a finite number of distinct values. Digital signals are not continuous signals. In the digital electronic calculator, the input is given with the help of switches. This input is converted into electrical signal which have two discrete values or levels. One of these may be called low level and another is called high level. The signal will always be one of the two levels. This type of signal is called digital signal. Examples of the digital signal are following.
- Binary Signal
- Octal Signal
- Hexadecimal Signal
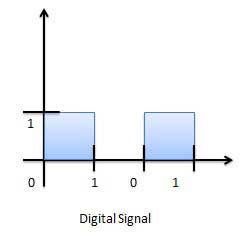
Graphical representation of the Digital Signal (Binary)
The circuits that process the digital signals are called digital systems or digital circuits. Examples of the digital systems are following.
- Registers
- Flip-flop
- Counters
- Microprocessors
Advantage of Digital Systems
- More accuracy
- More versatility
- Less distortion
- Easy communicate
- Possible storage of information
Comparison of Analog and Digital Signal
| S.N. | Analog Signal | Digital Signal |
|---|---|---|
| 1 | Analog signal has infinite values. | Digital signal has a finite number of values. |
| 2 | Analog signal has a continuous nature. | Digital signal has a discrete nature. |
| 3 | Analog signal is generated by transducers and signal generators. | Digital signal is generated by A to D converter. |
| 4 | Example of analog signal − sine wave, triangular waves. | Example of digital signal − binary signal. |